Operational resilience is the ability of an institution to deliver critical operations through disruptions. In March 2021, the Basel Committee, seeking to promote a principles-based approach to improving operational resilience, published its Principles for operational resilience.
Directed towards banks, the principles were largely derived from the existing guidance on outsourcing, business continuity and risk management-related guidance issued by the committee and built upon the committee’s Principles for the sound management of operational risk (PSMOR).
The Basel Committee’s framework consists of the following principles:
- Banks should utilise their existing governance structure to establish, oversee and implement an effective operational resilience approach that enables them to respond and adapt to, as well as recover and learn from, disruptive events in order to minimise their impact on delivering critical operations through disruption.
- Banks should leverage their respective functions for the management of operational risk to identify external and internal threats and potential failures in people, processes and systems on an ongoing basis, promptly assess the vulnerabilities of critical operations and manage the resulting risks in accordance with their operational resilience approach.
- Banks should have business continuity plans in place and conduct business continuity exercises under a range of severe but plausible scenarios in order to test their ability to deliver critical operations through disruption.
- Once a bank has identified its critical operations, the bank should map the internal and external interconnections and interdependencies that are necessary for the delivery of critical operations consistent with its approach to operational resilience.
- Banks should manage their dependencies on relationships, including those of, but not limited to, third parties or intragroup entities, for the delivery of critical operations.
- Banks should develop and implement response and recovery plans to manage incidents that could disrupt the delivery of critical operations in line with the bank’s risk appetite and tolerance for disruption. Banks should continuously improve their incident response and recovery plans by incorporating the lessons learned from previous incidents.
- Banks should ensure resilient ICT, including cybersecurity, that is subject to protection, detection, response and recovery programmes that are regularly tested, incorporate appropriate situational awareness and convey relevant timely information for risk management and decision-making processes to fully support and facilitate the delivery of the bank’s critical operations.
Following on from this, the two most widely known regimes for operational resilience are contained in the EU’s Regulation (EU) 2022/2554 (Digital Operational Resilience – DORA) and the UK’s operational resilience. These frameworks, broadly, mirror the Basel Committee’s Principles, but extend the scope to include a wide range of financial entities. However, several other jurisdictions have likewise devised their own operational resilience framework.
This regulatory influencer examines operational resilience standards in the EU and UK, alongside those in Australia, Singapore, Hong Kong and Malaysia, while benchmarking each jurisdiction’s approach against the EU's requirements.
Global Operational Resilience Requirements
|
Country
|
Requirements
|
Additional materials
|
|
European Union
|
Regulation (EU) 2022/2554 (Digital Operational Resilience Act – DORA)
The EU’s DORA lays down uniform requirements concerning the security of network and information systems supporting the business processes of financial entities. It applies to a large majority of financial institutions, including but not limited to:
- Credit institutions.
- Payment institutions, including payment institutions exempted pursuant to Directive (EU) 2015/2366 (revised Payment Services Directive – PSD2).
- Account information service providers.
- Electronic money institutions.
- Crypto-asset service providers.
- Trading venues.
- Management companies.
DORA lays down uniform requirements concerning the security of network and information systems supporting the business processes of financial entities. The regulation provides:
- Requirements applicable to financial entities in relation to ICT risk management, reporting, testing information sharing and measures for the sound management of ICT third-party risk.
- Requirements relating to the contractual arrangements concluded between ICT third-party service providers and financial entities.
- Rules for the establishment and conduct of the oversight framework for critical ICT third-party service providers when providing their services to financial entities.
- Rules for cooperation among competent authorities.
DORA provides several requirements for financial institutions to:
- Have in place an internal governance and control framework that ensures an effective and prudent management of ICT risk. Additionally, the management body of the financial entity must define, approve, oversee and be responsible for the implementation of all arrangements related to the ICT risk management framework.
- Have a sound, comprehensive and well-documented ICT risk management framework as part of their overall risk management system.
- Use and maintain updated ICT systems, protocols and tools.
- Identify, classify and adequately document all ICT supported business functions, roles and responsibilities, the information assets and ICT assets supporting those functions, and their roles and dependencies in relation to ICT risk.
- Continuously monitor and control the security and functioning of ICT systems and tools and minimise the impact of ICT risk on ICT systems through the deployment of appropriate ICT security tools, policies and procedures.
- Have in place mechanisms to promptly detect anomalous activities.
- Put in place a comprehensive ICT business continuity policy, which may be adopted as a dedicated specific policy, forming an integral part of the overall business continuity policy of the financial entity.
- Have in place capabilities and staff to gather information on vulnerabilities and cyber threats, ICT-related incidents, in particular cyber-attacks, and analyse the impact they are likely to have on their digital operational resilience.
- Have in place crisis communication plans enabling a responsible disclosure of, at least, major ICT-related incidents or vulnerabilities to clients and counterparts, as well as to the public, as appropriate.
- Define, establish and implement an ICT-related incident management process to detect, manage and notify ICT-related incidents.
- Classify ICT-related incidents and determine their impact.
- Report major ICT-related incidents to the relevant competent authority.
- Manage ICT third-party risk as an integral component of ICT risk within their ICT risk management framework. As part of this, financial entities must maintain and update at entity level, and at sub-consolidated and consolidated levels, a register of information in relation to all contractual arrangements on the use of ICT services provided by ICT third-party service providers.
- Clearly allocate the rights and obligations of the financial entity and of the ICT third-party service provider in writing.
- Establish, maintain and review a comprehensive digital operational resilience testing programme. This includes performing basic tests (such as vulnerability assessments and network security assessments) regularly, and for designated significant financial entities, conducting advanced threat-led penetration testing (TLPT) at least every three years.
- Set up arrangements to participate in voluntary information-sharing arrangements to exchange cyber threat information and intelligence with other financial entities, ensuring this is done within trusted communities to enhance collective resilience.
|
Mapping EU Legislation: Regulation (EU) 2022/2554 (Digital Operational Resilience Act – DORA) and Directive (EU) 2022/2556
Regulatory Reporting: Regulation (EU) 2022/2554 (Digital Operational Resilience Act – DORA) – Register of Information
Joint Guidelines (JC 2024 36) on the oversight cooperation and information exchange between the ESAs and the competent authorities under Regulation (EU) 2022/2554
Joint Guidelines (JC 2024 34) on the estimation of aggregated annual costs and losses caused by major ICT-related incidents under Regulation (EU) 2022/2554
Joint Guidelines (JC 2025 29) on oversight activities
European Banking Authority - Digital Operational Resilience Act
|
|
United Kingdom
|
Operational resilience
Primarily contained in the Financial Conduct Authority (FCA) Handbook’s SYSC 15A and in the Prudential Regulation Authority’s (PRA) rulebook for solo or dual regulated firms respectively, the UK’s operational resilience rules apply to:
- Enhanced scope SM&CR firms.
- Banks.
- Designated investment firms.
- Building societies.
- Solvency II firms.
- Payment and electronic money institutions.
- Registered account information service providers.
- Recognised investment exchanges.
As a primer, firms must identify their important business services. This is defined as a service provided by a firm to one or more clients of the firm which, if disrupted, could:
- Cause intolerable levels of harm to any one or more of the firm's clients.
- Pose a risk to the soundness, stability or resilience of the UK financial system or the orderly operation of the financial markets.
From there, a firm must, for each of its important business services, set an impact tolerance. This is defined as the maximum tolerable level of disruption to an important business service, as measured by a length of time in addition to any other relevant metrics, reflecting the point at which any further disruption to the important business service could cause intolerable harm to any one or more of the firm’s clients or pose a risk to the soundness, stability or resilience of the UK financial system or the orderly operation of the financial markets.
Next, a firm must ensure it can remain within its impact tolerance for each important business service in the event of a severe but plausible disruption to its operations.
Then, a firm must identify and document the people, processes, technology, facilities and information necessary to deliver each of its important business services. This must be sufficient to allow the firm to identify vulnerabilities and remedy these as appropriate.
Finally, a firm must develop and keep up to date a testing plan, with specific scenario tests, which appropriately details how it will gain assurance that it can remain within the impact tolerances for each of its important business services.
Following on from the testing or, in the event of an operational disruption, conduct a lessons learned exercise that allows the firm to identify weaknesses and take action to improve its ability to effectively respond and recover from future disruptions.
Aside from those requirements, firms must also maintain an internal and external communication strategy to act quickly and effectively to reduce the anticipated harm caused by disruptions.
Further, on December 13, 2024, the FCA and PRA launched a consultation (Consultation Paper (CP) 24/28) proposing new requirements for operational incident and third-party reporting.
Subsequently, on March 18, 2026, the PRA and FCA issued policy statements (FCA PS) (PRA PS) finalising the changes to the operational incidents and third-party reporting. The PSs set out a unified regulatory regime for operational incidents and third-party reporting to the FCA, PRA and Bank of England (BoE). The finalised rules set out reporting thresholds and relevant factors for consideration in operational incident reports, as well as notification requirements for material third-party arrangements.
|
PS26/2 - Operational Incident and Third-Party Reporting
SS1/26 – Operational Resilience: Incident Reporting
Operational resilience: insights and observations for firms
CrowdStrike outage: lessons for operational resilience
Effective practices: Cyber response and recovery capabilities
FCA Cyber Coordination Group Insights 2024
PS21/3 - Building operational resilience
Operational resilience: beyond regulatory raincoats
SS1/21 - Operational resilience: Impact tolerances for important business services
PRA - Operational resilience of the financial sector
SoP1/21 – Operational resilience
SS4/21 – Ensuring operational continuity in resolution
SS14/13 – Operational risk
Finalised guidance (FG) 26/3 – operational incident reporting
FG26/4 – Material third party reporting
|
|
Australia
|
Prudential Standard CPS 230
Australia’s CPS 230 aims to ensure that an Australian Prudential Regulation Authority (APRA) regulated entity is resilient to operational risks and disruptions.
This standard applies to:
- Authorised deposit-taking institutions.
- General insurers.
- Life companies.
- Private health insurers.
- Registrable superannuation entity licensees.
The standard outlines three key principles whereby an entity must:
- Effectively manage its operational risks and set and maintain appropriate standards for conduct and compliance.
- Maintain its critical operations within tolerance levels through severe disruptions.
- Manage the risks associated with the use of service providers.
As for the requirements of CPS 230, entities must:
- In relation to a risk management framework, develop and maintain:
- Governance arrangements.
- An assessment of their operational risk profile.
- Internal controls that are designed and operating effectively for the management of operational risks.
- Appropriate monitoring, analysis and reporting of operational risks and escalation processes.
- Business continuity plans (BCPs).
- Processes for the management of service provider arrangements.
- In relation to roles and responsibilities, the board of an APRA-regulated entity is ultimately accountable for oversight of an entity’s operational risk management. This includes business continuity and the management of service provider arrangements. Additionally, senior management of an APRA-regulated entity must provide clear and comprehensive information to the board on the expected impacts on the entity’s critical operations when the board is making decisions that could affect the resilience of critical operations.
- In relation to operational risk management, manage their full range of operational risks, including but not limited to legal risk, regulatory risk, compliance risk, conduct risk, technology risk, data risk and change management risk. Senior management are responsible for operational risk management across the end-to-end process for all business operations. Additionally, an APRA-regulated entity must maintain appropriate and sound information and IT capability to meet its current and projected business requirements and to support its critical operations and risk management.
- In relation to business continuity:
- Define, identify and maintain a register of critical operations.
- Take reasonable steps to minimise the likelihood and impact of disruptions to critical operations.
- Maintain a credible BCP that sets out how they would maintain critical operations within tolerance levels through disruptions, including disaster recovery planning for critical information assets.
- Activate their BCP if needed in the event of a disruption.
- Return to normal operations promptly after a disruption is over.
- In relation to management of service provider arrangements, maintain a comprehensive service provider management policy. The policy must cover how the entity will identify material service providers and manage service provider arrangements, including the management of material risks associated with the arrangements.
|
Prudential Practice Guide CPG 230 - Operational Risk Management
APRA operational risk management
|
|
Singapore
|
Multiple guidelines
According to the Monetary Authority of Singapore (MAS), operational resilience, which applies to all financial institutions, rests on four key pillars:
- Implementing a robust governance structure and appropriate risk appetite.
- Extending such oversight to external dependencies when third-party service providers are used.
- Managing cyber threats, system failures and digital transformation risks that could affect business operations or compromise third-party service providers.
- Planning well for business continuity that includes response and recovery measures which account for operational disruptions, third-party failures and technology incidents.
Singapore’s operational resilience framework consists of several guidelines and notices:
Operational risk management:
- Guidelines on operational risk management – the guidelines set out the key elements expected of an institution’s operational risk management framework and include guidelines on business continuity and outsourcing.
Technology and cyber risk management:
- Notices on technology risk management – several notices providing requirements that financial institutions have to comply with for a high level of reliability, availability and recoverability of critical IT systems and to implement IT controls to protect customer information from unauthorised access or disclosure.
- Notices on cyber hygiene – several notices providing requirements that financial institutions have to comply with for the purposes of managing cyber hygiene on securing administrative accounts, applying security patching, establishing baseline security standards, deploying network security devices, implementing anti-malware measures and strengthening user authentication.
- Guidelines on technology risk management – set out technology risk management principles and best practices on maintaining cyber resilience, establishing sound and robust technology risk governance and oversight.
Third-party risk management:
Businesses continuity management:
Through the guidelines and notices, financial institutions (FIs) are required to minimise the occurrence of disruptions, as well as to minimise their impacts if such disruptions occur. To accomplish this, FIs should have the ability to deliver critical business services and functions in the event of a disruption. Specifically, an operationally resilient institution should, at a minimum, be able to:
- Identify and prepare itself for both internal and external threats, as well as potential operational risk related events.
- Respond and recover from operational disruption swiftly and safely to resume critical business services and functions within recovery time objectives.
- Learn from potential operational risk-related events, operational disruptions, and near-misses with a view to enhance risk management practices.
In addition, as of March 2026, the MAS is consulting on its proposed guidelines on third-party risk management, as well as on updated guidelines on operational risk management.
In respect of the proposed guidelines on third-party risk management, the guidelines provide for:
- Expanded scope of third-party oversight, including extending existing outsourcing expectations to cover all third-party arrangements used by FIs, while emphasising that responsibility for service delivery, regulatory compliance and risk management remains with the FI and its board and senior management.
- Governance and risk-management responsibilities, requiring boards and senior management to establish and oversee a third-party risk management framework aligned with the FI’s overall risk management strategy and risk appetite, and to maintain a consolidated view of risks arising from third-party arrangements across the organisation and its branches or subsidiaries where applicable.
- A lifecycle approach to third-party arrangements covering risk assessment, due diligence, contracting, onboarding and ongoing monitoring, and termination, with expectations that FIs identify and assess financial and non-financial risks prior to entering into arrangements and continue monitoring such risks throughout the relationship.
Meanwhile, the draft updated guidelines on operational risk management include proposed updates to:
- Risk-proportionate implementation, which would apply to all financial institutions, but may be implemented proportionately based on the institution’s size, complexity and operational risk profile.
- Public disclosure requirements mandating domestic systemically important banks to publicly disclose their approach to operational risk management, operational risk exposures and their code of conduct to promote transparency and market discipline.
- Change management expectations under which financial institutions would be required to establish robust change management processes to identify and assess operational risks arising from new products, services, systems or market expansion.
- Oversight of branches and subsidiaries where financial institutions subject to consolidated supervision or that own critical information infrastructure would be expected to incorporate the operational risks of their branches and subsidiaries, including those located overseas, into their operational risk management framework.
|
Achieving Operational Resilience for Financial Institutions in Singapore
|
|
Hong Kong
|
Supervisory policy manual
Hong Kong’s operational resilience requirements are contained in the Hong Kong Monetary Authority's (HKMA) supervisory policy manual. Set out in OR-2, its requirements apply to all authorised institutions (AIs).
The manual outlines the HKMA’s expectation that all AIs must be operationally resilient. This is achieved where an AI is able to satisfy all of the following requirements:
- Identify and mitigate risks that may threaten delivery of critical operations.
- Continue to deliver critical operations when disruptions occur, including under severe but plausible scenarios.
- Resume normal operations in a timely manner after disruptions occur.
- Absorb learnings from disruptions or near misses.
Core to this is the development of an operational resilience framework that includes the following components:
- Mechanism for determining the operational resilience parameters, namely critical operations, tolerance for disruption and severe but plausible scenarios.
- Mapping exercises which enable an AI to develop a detailed understanding of the interconnections and interdependencies that underlie critical operations delivery.
- Risk management policies and frameworks that help an AI prepare for and manage the various risks to critical operations delivery in an integrated and holistic way.
- Scenario testing which enables an AI to regularly assess whether it is able to continue delivering critical operations through disruption, including under severe but plausible scenarios.
- An incident management programme which allows an AI to effectively respond to and manage disruptions to critical operations delivery.
Of note, the board is ultimately responsible for approving an AI’s operational resilience framework and for overseeing its implementation.
|
Business Continuity Planning
Good industry practices for implementing operational resilience
|
|
Malaysia
|
Business Continuity Management Policy Document
Applicable to financial institutions, the policy document sets out business continuity management (BCM) requirements, such being an integral pillar of operational resilience.
A financial institution in the policy document refers to:
BCM in the policy document entails an enterprise-wide framework, policies and processes that enable financial institutions to respond, recover and resume operations of critical business functions from operational disruptions that arise from internal or external risk events.
The policy document sets out the following requirements:
- That the board and senior management are responsible for the effective oversight and implementation of the BCM framework that is integrated with the overall risk management framework of the financial institution.
- Financial institutions must undertake risk assessments (RAs), business impact analysis (BIA) and identify their critical business functions (CBFs) and establish priorities for recovery.
- Based on the RA and BIA performed, financial institutions must determine business continuity objects for the CBFs, and must ensure continued availability of essential services during a disruption.
- Financial institutions must have in place a comprehensive recovery strategy.
- Based on the recovery strategy, a financial institution must formulate a robust and consistent crisis management plan (CMP), business continuity plan (BCP) and disaster recovery plan (DRP) to guide recovery actions for all CBFs.
- Financial institutions must formulate a crisis communication strategy and a crisis communication plan, which is incorporated in the CMP.
- Financial institutions must have in place processes to identify and assess various internal and external interdependencies.
- Financial institutions must maintain and safeguard critical business information records that are crucial in providing essential services.
- Financial institutions must have in place a rigorous testing program to evaluate the functionality and effectiveness of their BCM, readiness of staff and adequacy of resources in the event of a disruption.
- Financial institutions must submit notifications to Bank Negara Malaysia (BNM) for the occurrences of incidents.
However, on December 19, 2025, the BNM issued a discussion paper on operational resilience. The discussion paper outlines the BNM’s views on:
- Shifting to a resilience-first approach under which the BNM will move beyond traditional recovery focused models to a forward-looking approach that assumes disruptions are inevitable.
- Core principles of operational resilience which would obligate FIs to prioritise the continuity of critical operations and services, map internal and external dependencies, manage third-party risks, set tolerances for disruption and assess resilience through severe but plausible scenario testing.
- Malaysia’s existing regulatory context, including the BNM’s views on existing policy frameworks on business continuity management, technology risk management, outsourcing, operational risk and governance that already incorporate elements of operational resilience but may be further strengthened or integrated into a clearer resilience framework.
- Governance and accountability where the BNM expects the board and senior management of FIs to play a central role in overseeing operational resilience, including identifying critical services, approving disruption tolerances and ensuring adequate recovery capabilities.
- Industry challenges and trade-offs, including highlighting practical challenges, such as balancing resilience investments with cost pressures, managing reliance on third-party service providers, aligning incentives within institutions, and addressing systemic risks arising from shared infrastructure and interconnected financial services.
- Future regulatory direction where the BNM states it is considering whether to introduce a clearer articulation of operational resilience within the existing regulatory framework or develop a standalone operational resilience framework to guide financial institutions.
|
To the best of Vixio’s knowledge, Malaysian regulators have not provided any guidance documents.
|
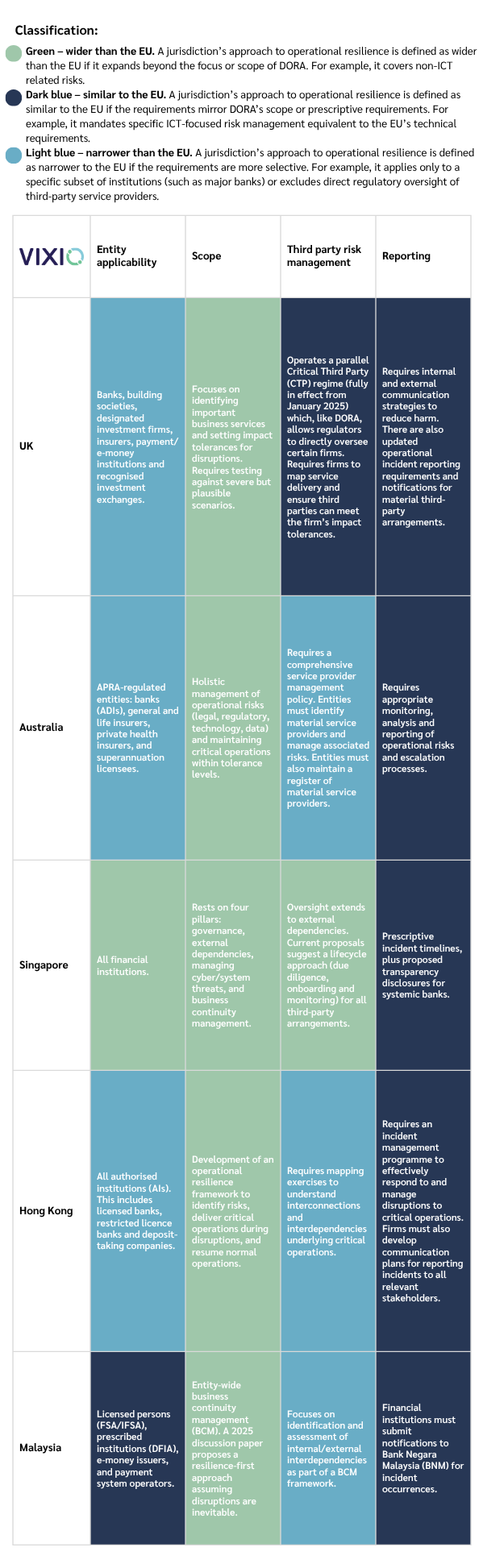
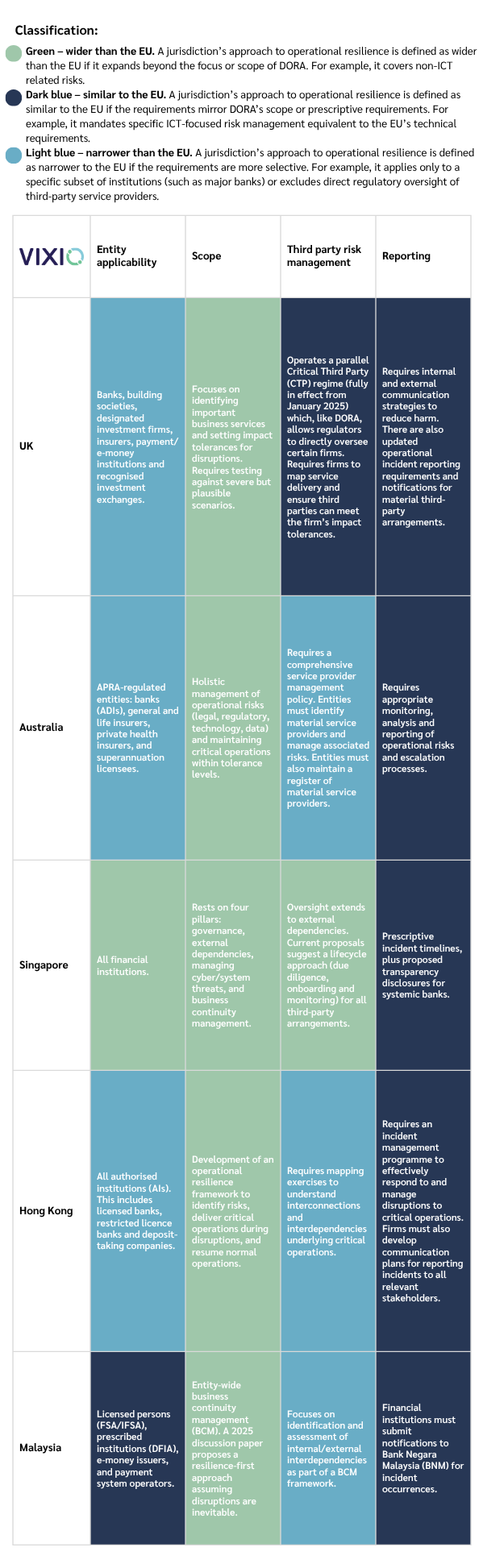
DORA vs the World - Comparative Overview (table can be downloaded here)
| |
Entity applicability
|
Scope
|
Third-party risk management
|
Reporting
|
|
EU
|
Applies to a large majority of financial institutions, including credit institutions, payment institutions, e-money institutions, crypto-asset service providers, trading venues, and management companies.
|
Uniform requirements for the security of network and information systems (ICT). Includes ICT risk management frameworks, digital resilience testing and information sharing.
|
Rules for contractual arrangements between ICT third-party providers and financial entities. Establishes an oversight framework specifically for critical ICT third-party service providers.
|
Requires reporting of major ICT-related incidents to relevant competent authorities. Requires crisis communication plans for disclosure to clients and the public. Mandates internal/external communication strategies and a designated media spokesperson.
|
Several other jurisdictions have also created or are creating their own operational resilience frameworks, including:
Canada – Guideline E-21
Published on August 22, 2024 by the Office of the Superintendent of Financial Institutions (OSFI), the guideline sets out the regulator's expectation for financial institutions to prepare for and recover from severe disruptive events.
The guideline applies from September 1, 2026.
United Arab Emirates – Operational Risk Regulation
Published on August 29, 2018, the Operational Risk Regulation (ORR) establishes minimum acceptable standards for banks’ approach to managing operational risks, with a view to:
- Ensure the soundness of banks.
- Enhance financial stability.
The regulation entered into force on September 29, 2018.
Separately, the Dubai Financial Financial Services Authority (DFSA) and the Abu Dhabi Global Market’s Financial Services Regulatory Authority (FSRA) have distinct operational resilience frameworks.
United States – Regulator issued guidelines
The United States does not have a comparable, unified operational resilience framework. Instead, individual regulators have issued operational resilience guidance.
For instance, the Board of Governors of the Federal Reserve System has issued the following:
- SR 24-5 – Joint Statement on Banks’ Arrangements with Third Parties to Deliver Bank Deposit Products and Services.
- SR 24-2 / CA 24-1 – Third-Party Risk Management: A Guide for Community Banks.
- SR 23-4 – Interagency Guidance on Third-Party Relationships: Risk Management.
- SR 22-4 / CA 22-3 – Contact Information in Relation to Computer-Security Incident Notification Requirements.
- SR 20-24 – Interagency Paper on Sound Practices to Strengthen Operational Resilience.
South Africa – D4/2023: Principles for operational resilience
Issued in the form of a directive, the document outlines principles for operational resilience, applicable to banks, including:
- Governance.
- Operational risk management.
- Business continuity planning and testing.
- Mapping of interconnections and interdependencies of critical operations.
Banks were mandated to comply with the operational resilience requirements by December 31, 2024.
Peru – Superintendencia de Banca (SBS) Resolutions
Peru’s operational resilience framework is made up of two resolutions:
Collectively, the resolutions provide for Peru’s operational resilience requirements which apply to:
- Banks.
- Financial institutions.
- Savings and credit local institutions.
- Small businesses and micro-enterprise development companies.
- Specialised companies.
- Investment banks.
- Insurance companies.



.svg)



